SOC 2 Type 1 vs Type 2 and why Type 2 is where AI automation matters
Type 1 proves your controls exist on paper. Type 2 proves they actually worked over months of real operation. Most enterprise buyers demand Type 2, and the evidence collection grind is where AI-assisted automation delivers real returns.
Key takeaways
- Type 1 is a snapshot - proves controls exist at a single point in time
- Type 2 covers months - proves controls worked consistently over an observation period
- Type 2 is where automation pays off - quarterly evidence collection across 123 items benefits from AI assistance
- Most customers require Type 2 - Type 1 is a stepping stone, not the destination
Type 1 proves controls exist on paper. Type 2 proves they work over months. That’s the entire distinction, but the implications are enormous.
If you run a SaaS company selling to mid-market or enterprise customers, your prospects don’t care about your intentions. They care whether your security controls actually operated the way you said they would, consistently, across a sustained period. That’s the difference between passing a written driving test and proving you can drive safely for six months straight.
At Tallyfy, we’ve been through multiple Type 2 audit cycles. The first one taught us something that no compliance platform sales demo ever mentioned: the hard part isn’t designing controls. It’s collecting evidence that those controls kept working, quarter after quarter, for an entire observation period.
What each type actually tests
The AICPA’s Trust Services Criteria framework defines two examination approaches, and they test fundamentally different things. If you need a grounding in what SOC 2 actually is, start there.
A Type 1 report evaluates the design of your controls at a single point in time. Think of it as an inspector walking through your building and confirming that fire extinguishers are mounted on the walls, exit signs are lit, and sprinkler systems are installed. Everything looks right on the day of the inspection. The auditor verifies that your controls exist, are properly designed, and could work. That’s it. One day. One snapshot.
A Type 2 report evaluates both the design and the operating effectiveness of those controls over an extended period. Same inspector, but now they’re reviewing six to twelve months of fire alarm test logs, sprinkler maintenance records, and evacuation drill reports. Did the controls actually function the way they were supposed to, repeatedly, over time?
Cherry Bekaert’s audit guidance makes the timeline distinction clear. Type 1 can wrap up in weeks because the auditor only needs to examine controls as they exist right now. Type 2 requires an observation window of three to twelve months because the auditor needs to sample evidence across that entire stretch. The AICPA doesn’t mandate a specific minimum observation period, but most auditing firms won’t accept anything shorter than three months, and six months is the standard recommendation for a first-time Type 2 engagement.
Our current audit period runs from March 2025 through February 2026. A full twelve months. That means every control we claim to operate needs evidence stretching across that entire year.
audit_period_start: '2025-03-01'
audit_period_end: '2026-02-28'The observation period problem
Here’s where it gets real. Type 1 is relatively painless because you only need to demonstrate controls once. You collect your evidence, hand it to the auditor, and you’re done. Type 2 asks you to prove those same controls functioned over months.
Consider what that actually means in practice. Your access review policy says you review user access quarterly. For Type 2, the auditor doesn’t just want to see that you have a policy. They want evidence of four quarterly reviews across the observation period. Your vulnerability scanning policy says you scan monthly. The auditor wants twelve months of scan reports. Your employee termination procedure says you remove access within 24 hours. They want evidence from every termination during the observation period showing timely removal.
This creates a compounding problem. Miss one quarterly review and you have a gap. Forget to save a scan report and you have incomplete evidence. Terminate an employee on Friday and don’t remove access until Monday and you have a potential finding.
CPA analysis of Type 2 requirements highlights that this ongoing evidence burden is exactly why Type 2 reports carry significantly more weight with enterprise buyers. A Type 1 tells them you built the house. A Type 2 tells them you actually live in it and maintain it. Practitioner research confirms what we’ve experienced firsthand: most security and procurement teams use your SOC 2 Type 2 report as a shortcut to complete their internal vendor risk questionnaire. Without it, you’re filling out lengthy security questionnaires for every prospect, which slows deals by weeks.
The reality for SaaS founders is blunt. Type 1 is a stepping stone. It might satisfy early customers, but as you move upmarket, enterprise buyers expect Type 2. It’s not optional. It’s a prerequisite to even being considered.
Why evidence collection frequency matters for Type 2
Not all evidence is created equal, and not all of it needs to be collected at the same cadence. This was one of the less obvious lessons from running a compliance program without a traditional platform.
Our evidence requirements break down into frequency tiers:
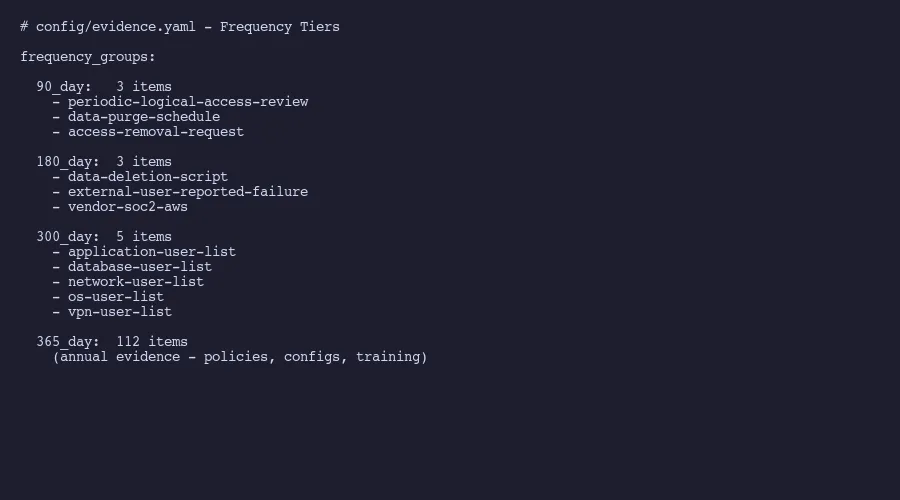 Evidence collection frequency tiers from our evidence.yaml
Evidence collection frequency tiers from our evidence.yaml
Evidence collection frequency tiers:
- 90-day: 3 items (access reviews, data purge, access removal)
- 180-day: 3 items (data deletion, external failures, vendor SOC 2)
- 300-day: 5 items (user lists across all systems)
- 365-day: 112 items (annual evidence)That’s 123 total evidence items. The 90-day items are the most operationally demanding because they need to be collected four times during a twelve-month observation period. Forget one cycle and you’ve created a gap that your auditor will flag.
The 365-day items look deceptively simple since they only need collection once per year. But 112 items in a single pass is a lot. Screenshots of AWS configurations. Exports from identity providers. Policy acknowledgement records. Firewall rule documentation. Encryption settings across every system in scope.
CPA analysis of evidence review cadence makes a point that resonates with our experience: most SOC 2 delays aren’t caused by missing tools. They come from a lack of clarity about when evidence needs to be collected and who owns each item. The cadence matters as much as the collection itself.
Evidence staleness is the silent killer of Type 2 audits. A screenshot of your password policy from month two of a twelve-month observation period doesn’t prove that policy was still in effect during month eleven. Auditors sample across the entire period. Linford’s guidance on monitoring activities explains that auditors place the highest trust in evidence collected directly from the systems where controls operate, and they want to see that collection happened at appropriate intervals throughout the observation window.
Where AI automation changes the math
Here’s where I’ll be direct about what we’ve been doing at Tallyfy instead of paying for a compliance platform.
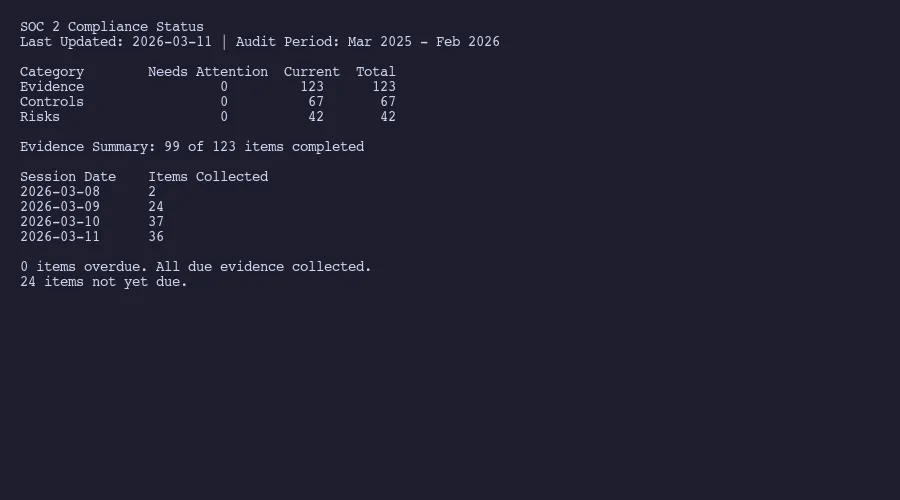 Our compliance status dashboard showing 99 of 123 items collected across 4 sessions
Our compliance status dashboard showing 99 of 123 items collected across 4 sessions
We collected 99 of 123 evidence items across 4 AI-assisted sessions in March 2026. That’s not a typo. Four focused sessions to gather the vast majority of our annual evidence. The remaining 24 items involve manual steps like taking specific screenshots that require navigating authenticated admin panels or collecting documents from external vendors.
The AI assistance works at the analysis and organization layer, not the collection layer. It reviews exported user lists against our control requirements. It cross-references access configurations against policy documents. It identifies gaps in evidence before the auditor does. It generates structured summaries that map evidence to specific Trust Services Criteria points.
For the 90-day items, specifically access reviews, data purge verification, and access removal checks, AI processes the raw exports and highlights anomalies. A quarterly access review across five systems used to take half a day of comparing spreadsheets. Now it takes about twenty minutes because the analysis is automated while the judgment calls remain human.
CertPro’s research on automated evidence collection confirms a pattern we’ve seen. Automation doesn’t eliminate the work, but it compresses the tedious parts dramatically. The evidence still needs to exist. Someone still needs to configure the controls properly. The systems still need to be running correctly. What changes is how quickly you can verify and document that everything worked as intended. We wrote more about how automated evidence collection works in practice.
Type 1 audits don’t benefit much from this automation because you’re collecting evidence once and the volume is manageable. Type 2 is where it matters. When you’re maintaining evidence across quarterly cycles for an entire year, across 123 items with different collection frequencies, the organizational overhead is the bottleneck. That’s exactly the kind of structured, repetitive, high-volume work where AI assistance shines.
The frustrating truth about compliance is that it’s not intellectually hard. It’s operationally tedious. You know what needs to happen. You know when it needs to happen. You just have to actually do it, document it, and file it correctly, over and over, for months.
The practical path from Type 1 to Type 2
If you’re a SaaS company starting from scratch, here’s the path that makes sense based on actually walking it.
Start with Type 1 if you need something to show prospects now. It can be completed in weeks, costs significantly less, and gives you a report you can share during sales cycles. Jones IT’s startup guidance suggests that early-stage companies can use Type 1 as a bridge while building toward Type 2. Fair enough. But go in with eyes open about what Type 1 doesn’t prove.
Some companies skip Type 1 entirely and go straight to Type 2 with a shorter initial observation period. Three months is the practical minimum. Six months is safer for a first audit. This approach costs more upfront but gets you to the report that enterprise buyers actually want faster. CPA timeline guidance suggests engaging your CPA firm three to six months before you want the Type 2 observation period to begin.
Whatever path you choose, the moment your observation period starts, your evidence collection cadence becomes non-negotiable. Those 90-day items can’t slip. Those user list exports at 300 days can’t be forgotten. The 112 annual items can’t be left to the last week before the auditor arrives.
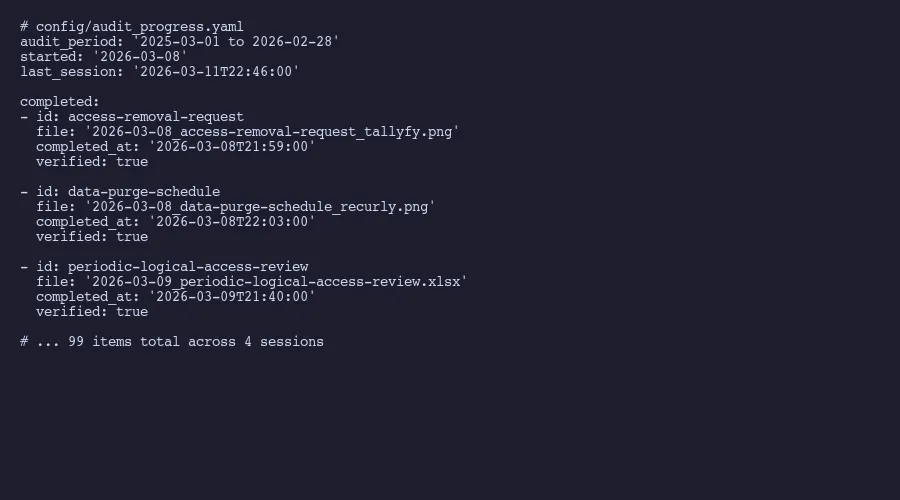 Audit progress tracking showing 4 collection sessions
Audit progress tracking showing 4 collection sessions
We track this in a structured YAML file that logs every collection session with timestamps, item counts, and remaining gaps. It’s not glamorous. It’s a file in a Git repository that gets updated after every collection session. But it creates an auditable trail of when evidence was gathered, and it gives us clear visibility into what’s outstanding.
The difference between companies that breeze through Type 2 audits and companies that scramble is rarely about the quality of their controls. It’s about the discipline of evidence collection. Build the cadence early. Automate the tedious parts. Keep the judgment calls human. That’s the formula that works, whether you use a compliance platform or, as we’ve found, a Git repository and AI.
About the Author
Amit Kothari is an experienced consultant, advisor, coach, and educator specializing in AI and operations for executives and their companies. With 25+ years of experience and as the founder of Tallyfy (raised $3.6m), he helps mid-size companies identify, plan, and implement practical AI solutions that actually work. Originally British and now based in St. Louis, MO, Amit combines deep technical expertise with real-world business understanding.
Disclaimer: The content in this article represents personal opinions based on extensive research and practical experience. While every effort has been made to ensure accuracy through data analysis and source verification, this should not be considered professional advice. Always consult with qualified professionals for decisions specific to your situation.